Since its launch in 2017, the IAB’s ads.txt initiative has brought increased transparency into the programmatic advertising ecosystem of sellers and domains.
One of the primary goals of the ads.txt program is to reduce counterfeit inventory, or domain spoofing — a specific type of ad fraud and invalid traffic (IVT). Domain spoofing occurs when a domain is misrepresented during a programmatic ad transaction — e.g. a low-quality publisher claiming to be a high-quality publisher. Spoofing makes the inventory appear more valuable, and this type of ad fraud costs marketers millions of dollars per year.
Ads.txt launched one year ago, and now that the majority of major publishers have implemented ads.txt, it’s time to review the initiative’s impact on ad fraud.
(Click here to download the full Q2 2018 Ads.txt Trends Report)
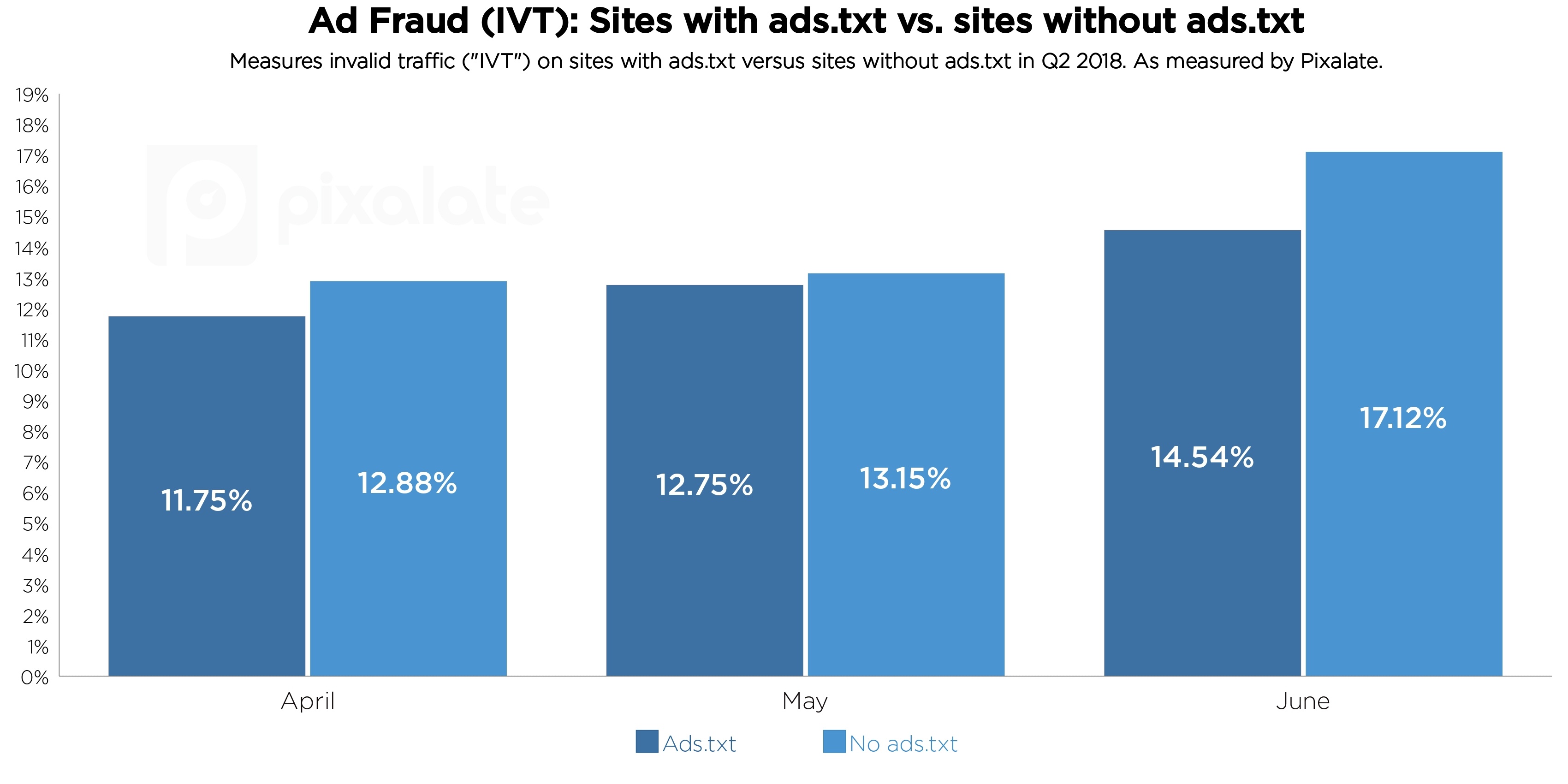
Pixalate analyzed industry-wide ads.txt data for our Q2 2018 Ads.txt Trends Report and found that, on average, sites with ads.txt have a 10% lower ad fraud rate compared to sites without ads.txt.
Our Q2 2018 data indicates that the positive impact of ads.txt may be growing, as evidenced by June’s 15% decrease, but more data over time is needed to confirm.
Ads.txt was designed to reduce “domain spoofing” in the open programmatic marketplace. Spoofing occurs when a domain is misrepresented during a programmatic ad transaction. Fraudsters can “spoof” premium publishers to make inventory appear more valuable.
Domain spoofing is a costly problem for marketers. The Financial Times investigated domain spoofing of their inventory — e.g. fraudsters claiming to be FT.com — and found that over $1.3 million worth of fraudulent inventory was traded per month.
Ads.txt directly protects against domain spoofing by enabling publishers to declare the companies that are authorized to sell their digital inventory. Each publisher’s ads.txt file serves as a public ledger that buyers can cross-reference to ensure that the inventory they are buying will go to the claimed domain.
As our data shows, even though sites with ads.txt have generally lower IVT rates, they are not fraud-free.
A major reason why is because ads.txt protects against just one type of ad fraud (domain spoofing). Pixalate tracks 38 unique types of ad fraud; there are still many other ways in which fraudsters are stealing budgets.
Bad intenders can also create ads.txt files on fraudulent domains to appear more legitimate. For example, Pixalate discovered a family of domains that hijacked sessions without malware, and many of the fraudulent domains had ads.txt files.
Additionally, ads.txt does not work across all formats, including mobile in-app. The IAB Tech Lab released a draft for public comment regarding mobile in-app ads.txt support in June 2018.
You can download the full list of domains with ads.txt here. This list is updated monthly.
You can also download our Q2 2018 Ads.txt Trends Report for a comprehensive update on the state of ads.txt adoption.
Want more data-driven insights? Sign up for our blog!
*By entering your email address and clicking Subscribe, you are agreeing to our Terms of Use and Privacy Policy.
These Stories on Research Reports
*By entering your email address and clicking Subscribe, you are agreeing to our Terms of Use and Privacy Policy.
Disclaimer: The content of this page reflects Pixalate’s opinions with respect to the factors that Pixalate believes can be useful to the digital media industry. Any proprietary data shared is grounded in Pixalate’s proprietary technology and analytics, which Pixalate is continuously evaluating and updating. Any references to outside sources should not be construed as endorsements. Pixalate’s opinions are just that - opinion, not facts or guarantees.
Per the MRC, “'Fraud' is not intended to represent fraud as defined in various laws, statutes and ordinances or as conventionally used in U.S. Court or other legal proceedings, but rather a custom definition strictly for advertising measurement purposes. Also per the MRC, “‘Invalid Traffic’ is defined generally as traffic that does not meet certain ad serving quality or completeness criteria, or otherwise does not represent legitimate ad traffic that should be included in measurement counts. Among the reasons why ad traffic may be deemed invalid is it is a result of non-human traffic (spiders, bots, etc.), or activity designed to produce fraudulent traffic.”

