Pixalate is an MRC-accredited company for the detection and filtration of Sophisticated Invalid Traffic ("SIVT") desktop and mobile web impressions.
According to the Media Rating Council’s (MRC) standards for Invalid Traffic Detection and Filtration Guidelines, there are two types of invalid traffic:
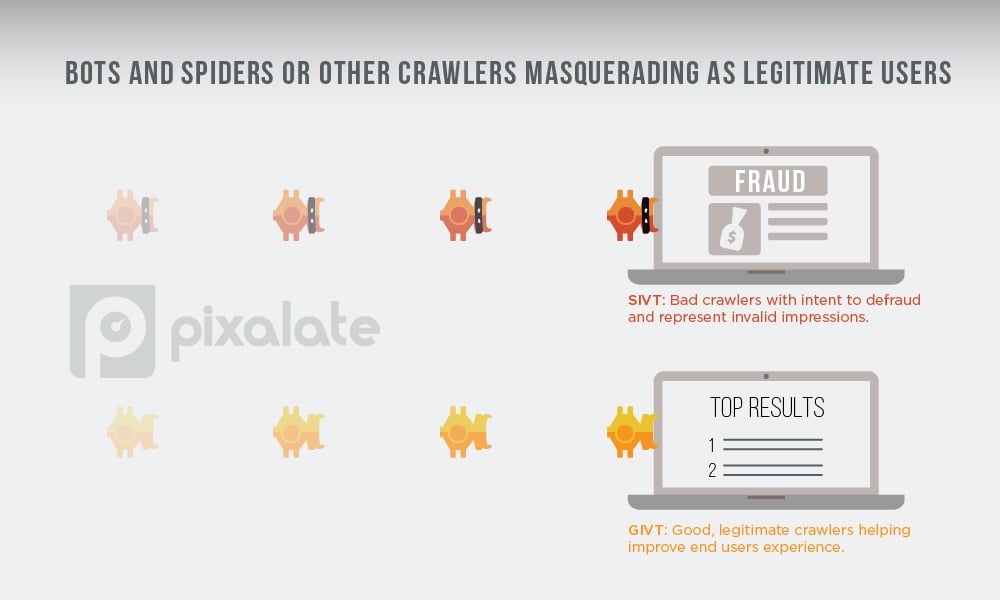
One example of SIVT is “bots and spiders or other crawlers masquerading as legitimate users.”
Bots and spiders or other crawlers represent non-human activity on the web. In some circumstances, these bots, spiders, or other crawlers are legitimate — e.g. “good” — but they are still non-human nonetheless. These “good” bots, spiders or crawlers are GIVT.
But there are “bad” bots, spiders, or crawlers that fall under the SIVT umbrella. Unlike known — e.g. “good” — crawlers, these crawlers may use standard browser identifiers.
If a crawler users standard browser identifiers, it means they are masquerading as a legitimate user. Web crawlers configured in this manner may occasionally serve a legitimate purpose such as testing page load times, but in many cases, the intent is to defraud and in both cases represent invalid impressions. Sophisticated analytics are employed to identify the signature of non-human crawlers operating in this manner.
MRC-accredited ad fraud detection and prevention companies must be able to identify and filter out bots, spiders, or other crawlers masquerading as legitimate users.
Bots and spiders or other crawlers masquerading as legitimate users is just one example of Sophisticated Invalid Traffic (SIVT) as defined by the MRC. To learn about some of the other examples of SIVT, click on any of the examples below:
*By entering your email address and clicking Subscribe, you are agreeing to our Terms of Use and Privacy Policy.
These Stories on Thought Leadership
*By entering your email address and clicking Subscribe, you are agreeing to our Terms of Use and Privacy Policy.
Disclaimer: The content of this page reflects Pixalate’s opinions with respect to the factors that Pixalate believes can be useful to the digital media industry. Any proprietary data shared is grounded in Pixalate’s proprietary technology and analytics, which Pixalate is continuously evaluating and updating. Any references to outside sources should not be construed as endorsements. Pixalate’s opinions are just that - opinion, not facts or guarantees.
Per the MRC, “'Fraud' is not intended to represent fraud as defined in various laws, statutes and ordinances or as conventionally used in U.S. Court or other legal proceedings, but rather a custom definition strictly for advertising measurement purposes. Also per the MRC, “‘Invalid Traffic’ is defined generally as traffic that does not meet certain ad serving quality or completeness criteria, or otherwise does not represent legitimate ad traffic that should be included in measurement counts. Among the reasons why ad traffic may be deemed invalid is it is a result of non-human traffic (spiders, bots, etc.), or activity designed to produce fraudulent traffic.”

