Pixalate has had many conversations lately with companies across the ad tech ecosystem about how to protect their OTT and Connected TV (OTT/CTV) media, and one subject in particular always comes up: Server-Side Ad Insertion (SSAI).
Pixalate firmly believes that invalid SSAI is the largest risk factor to OTT/CTV advertising. Using Magna’s most recent OTT ad spend forecasts and Pixalate’s analysis, invalid SSAI alone threatens millions in ad spend.
Despite these high numbers, the industry at large does not acknowledge that SSAI can be used for fraudulent purposes, and, upon learning of the dangers of SSAI, they don’t know what they can do to protect their investments.
Pixalate is here to help. We are publishing a series of blogs to take a deep dive into all things SSAI:
Click to see larger size
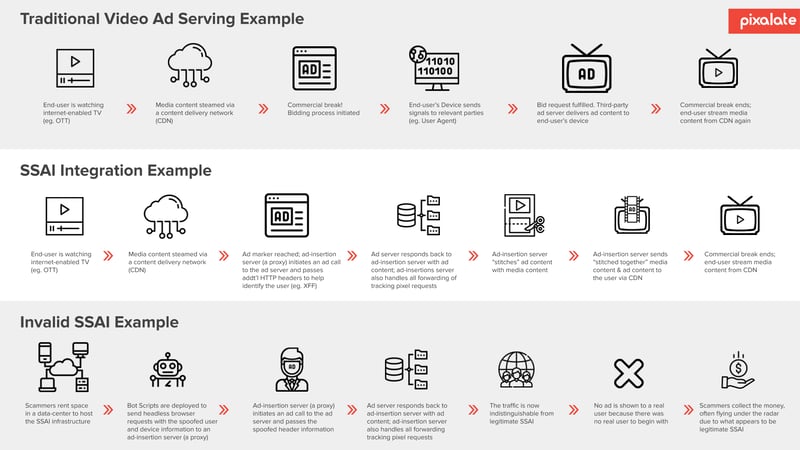
Server-side ad insertion (SSAI) — also referred to as “ad stitching,” “server-side ad stitching,” or “dynamic ad insertion” — is a method of programmatic ad delivery whereby ad content is delivered in union with the video content.
This is done by “stitching” the video ad with the video content at the server level to create a more seamless user experience.
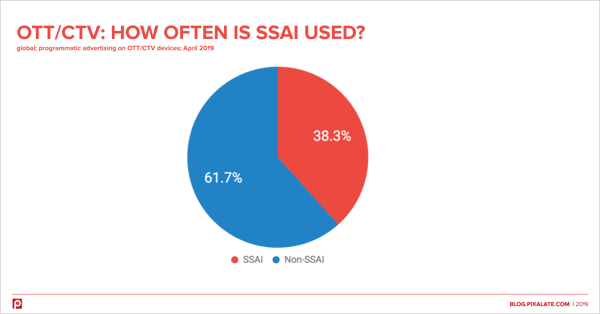
Over one-third (38%) of all programmatic OTT/CTV ad transactions are delivered via SSAI, according to Pixalate data.
In traditional client-side ad insertion, video content is obtained from a content delivery network (CDN) on the server-side, while ad content is obtained separately from a third-party ad server.
However, in SSAI, the video content and ad content are combined server-side via the ad-insertion server (or “SSAI server” as referenced throughout this article) which is responsible for employing the SSAI integration and delivering ad content in union with the publisher’s video content to the end-user’s device.
One common misconception regarding SSAI traffic is that such traffic is not as susceptible to exploitation by scammers. However, this is wholly inaccurate.
SSAI integrations are just as susceptible to ad fraud schemes as client-side ad insertion techniques. Furthermore, as a result of the shift in ad spend to OTT/CTV channels, SSAI integrations are being exploited on a large scale due to the tendency to fully whitelist SSAI servers.
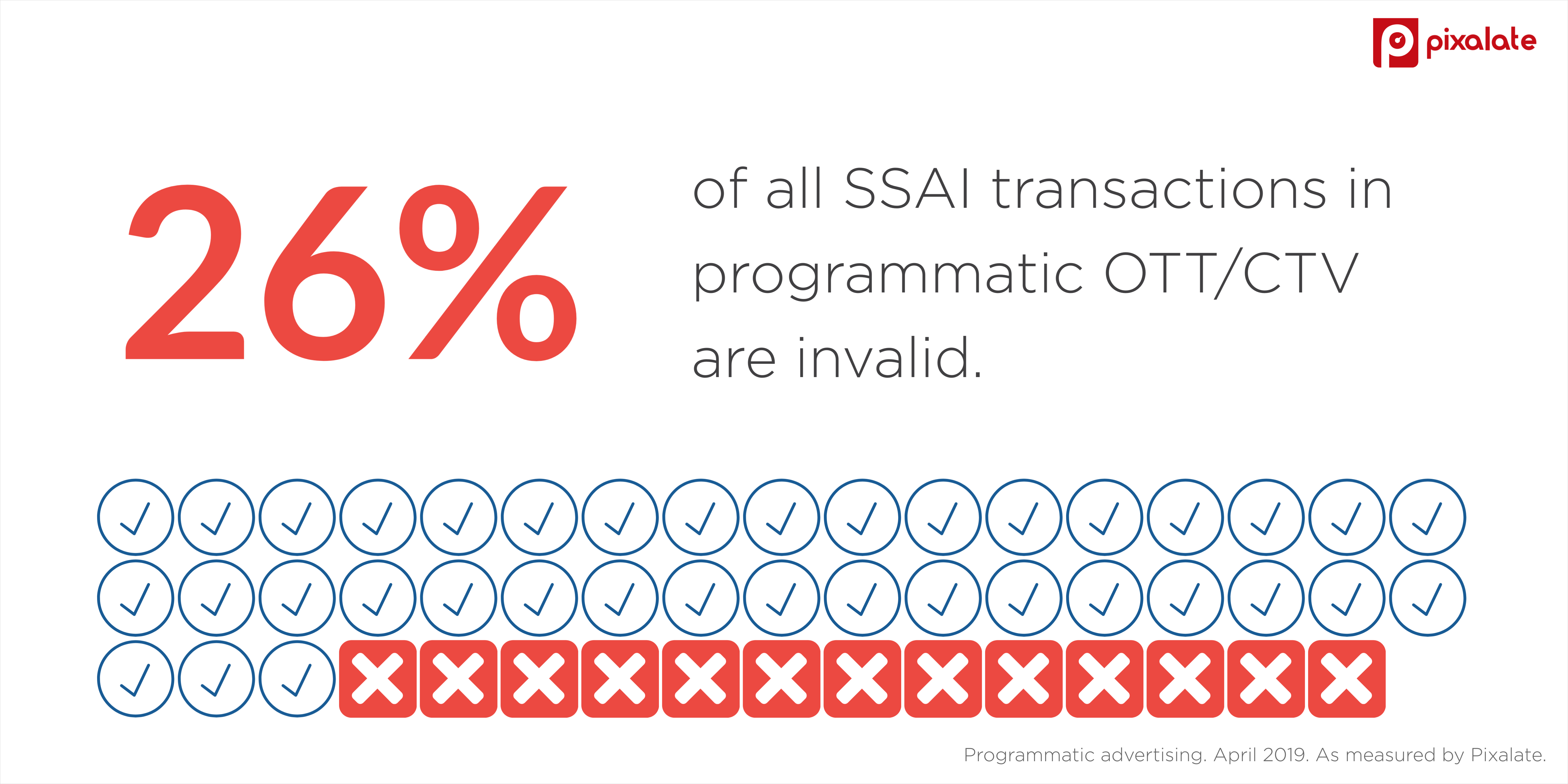
In fact, 26% of all SSAI used for OTT/CTV programmatic advertising is deemed invalid. If advertisers blindly trust all SSAI integrations, then they may be putting over one-fourth of their OTT/CTV budgets at risk.
Depending on the exact SSAI architecture used, it is possible that the entirety of user activity is represented/communicated by an SSAI proxy server responsible for composing HTTP requests on behalf of the end-user seeing the ad content.
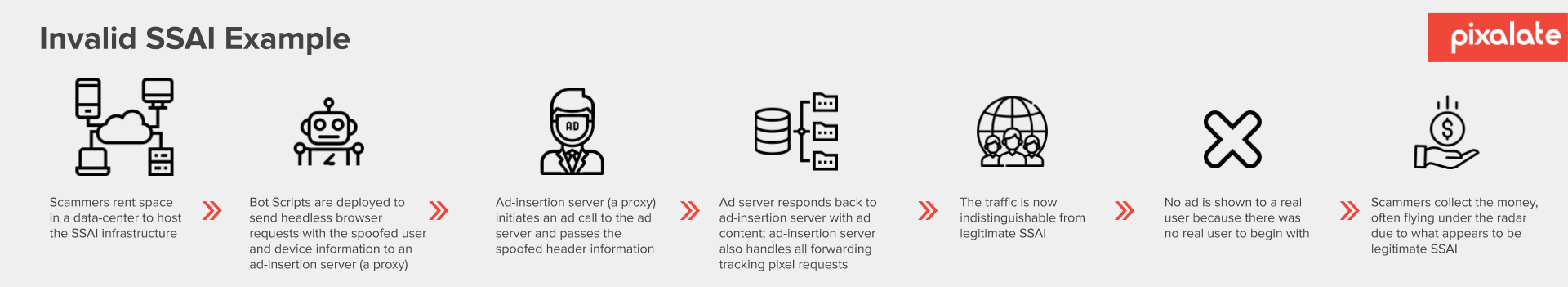 This opens a significant security gap to fraudsters, allowing them to use machines that mimic proxies to spoof the user request headers by faking all the associated HTTP header fields (e.g., X-Forwarded-For, X-Device-User-Agent, Forwarded HTTP extension, etc.).
This opens a significant security gap to fraudsters, allowing them to use machines that mimic proxies to spoof the user request headers by faking all the associated HTTP header fields (e.g., X-Forwarded-For, X-Device-User-Agent, Forwarded HTTP extension, etc.).
SSAI IPs are oftentimes wholly whitelisted by digital supply chain partners in an effort to avoid false positives in their ad fraud designations. This blanket whitelisting approach can facilitate the exploitation of SSAI integrations by scammers for purposes of perpetrating ad fraud.
Legitimate SSAI servers can also be exploited by fraudsters as these SSAI integrations merely serve as an additional layer of obfuscation/masking for fraudsters, thus re-emphasizing the industry need for dedicated sophisticated ad fraud detection and filtration vendors.
SSAI delivery is widely used across programmatic advertising, although it is most frequently used by providers of longer form video content and is most prevalent today in OTT/CTV.
SSAI was developed on the publisher sell-side as a technological solution to overcome certain video ad monetization challenges, namely user experience fails, device fragmentation, and ad blocking.
Pixalate, the first and currently only company accredited by the MRC for sophisticated invalid traffic (SIVT) detection and filtration in OTT/CTV, has gathered industry experts for a webinar on the use of Server-Side Ad Insertion (SSAI) in OTT/CTV advertising.
On Thursday, July 11, 2019 at 1:00pm ET, Pixalate Product Manager Chris Schwarz will host:
Register today!
Disclaimer
Although grounded in Pixalate’s proprietary technology and analytics (which Pixalate evaluates and updates continuously), invalid traffic (IVT) designations in this blog post represent Pixalate’s opinions (i.e., they are neither facts nor guarantees). Per the MRC, the term “'Fraud' is not intended to represent fraud as defined in various laws, statutes and ordinances or as conventionally used in U.S. Court or other legal proceedings, but rather a custom definition strictly for advertising measurement purposes;” and also per the MRC, “'Invalid Traffic' is defined generally as traffic that does not meet certain ad serving quality or completeness criteria, or otherwise does not represent legitimate ad traffic that should be included in measurement counts. Among the reasons why ad traffic may be deemed invalid is it is a result of non-human traffic (spiders, bots, etc.), or activity designed to produce fraudulent traffic.”
*By entering your email address and clicking Subscribe, you are agreeing to our Terms of Use and Privacy Policy.
These Stories on Thought Leadership
*By entering your email address and clicking Subscribe, you are agreeing to our Terms of Use and Privacy Policy.
Disclaimer: The content of this page reflects Pixalate’s opinions with respect to the factors that Pixalate believes can be useful to the digital media industry. Any proprietary data shared is grounded in Pixalate’s proprietary technology and analytics, which Pixalate is continuously evaluating and updating. Any references to outside sources should not be construed as endorsements. Pixalate’s opinions are just that - opinion, not facts or guarantees.
Per the MRC, “'Fraud' is not intended to represent fraud as defined in various laws, statutes and ordinances or as conventionally used in U.S. Court or other legal proceedings, but rather a custom definition strictly for advertising measurement purposes. Also per the MRC, “‘Invalid Traffic’ is defined generally as traffic that does not meet certain ad serving quality or completeness criteria, or otherwise does not represent legitimate ad traffic that should be included in measurement counts. Among the reasons why ad traffic may be deemed invalid is it is a result of non-human traffic (spiders, bots, etc.), or activity designed to produce fraudulent traffic.”

